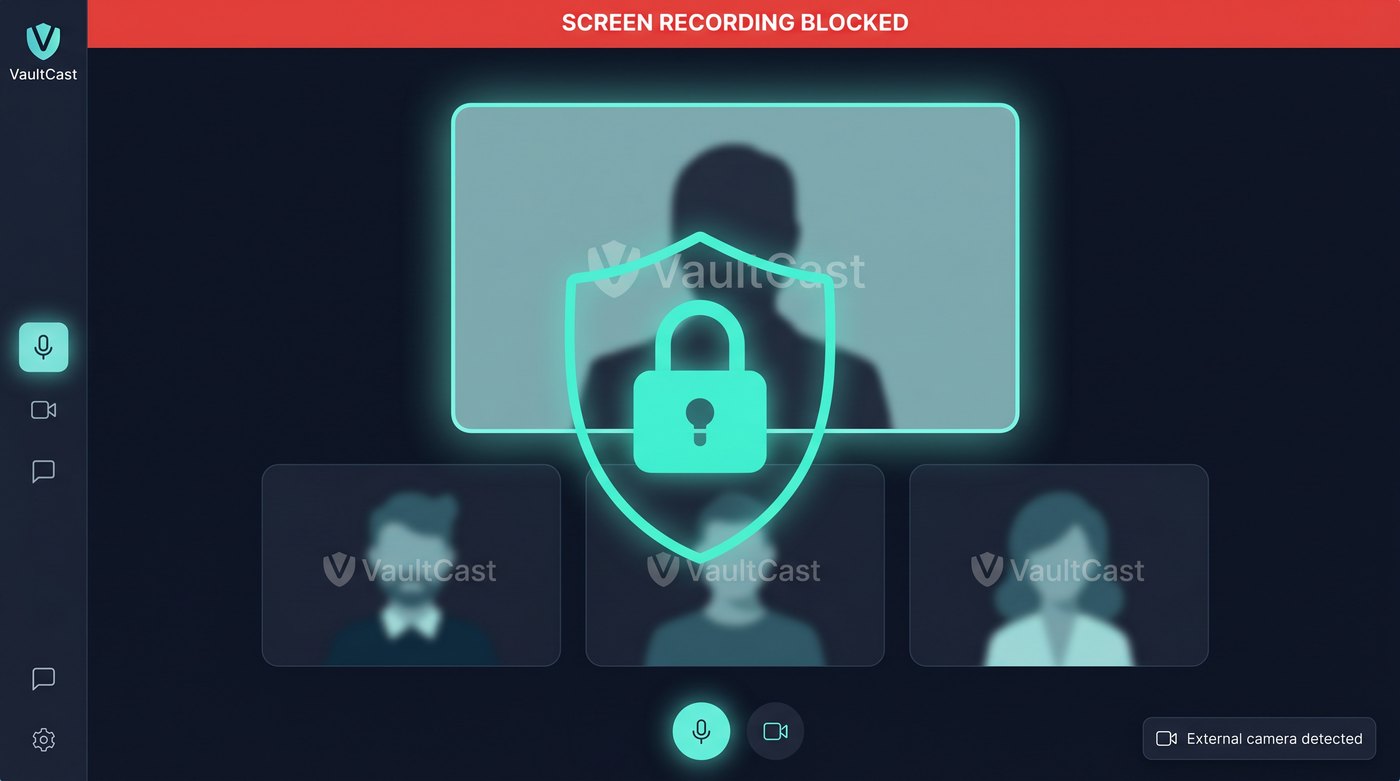
The problem
Standard video conferencing platforms leak. Screenshots, screen recordings, and second-camera capture of a participant’s screen are trivially easy. For sensitive meetings — buyer reviews, M&A discussions, confidential design previews — that’s a hard blocker.
The solution
VaultCast is built privacy-first from the protocol up. Every layer assumes someone will try to capture content, and makes it dramatically harder, traceable, or impossible.
Privacy & DRM layers
- Screenshot & screen-recording blocks at the OS level on Android, with policy enforcement on web.
- On-device AI detection — the front camera continuously analyses the participant’s field of view; if it detects another camera or phone recording the screen, the host is alerted in real time.
- Tier-based DRM — Widevine L1 enforced on supported devices for the highest-sensitivity streams; L3 fallback with watermark intensification for lower-trust hardware.
- Dynamic watermarking — every frame carries an invisible-when-still, visible-when-recorded watermark that ties leaked frames back to the specific participant and session.
- Hardened native Android shell — root detection, hook detection, debugger detection, frida-resistant runtime.
Stack
My role
End-to-end. I designed and shipped the backend, the web client, the native Android app, the DRM integration, and the on-device AI recording-detection model. From threat-modeling whiteboards to production CI/CD.